Data research project

Llanfairpwllgwyngyllgogerychwyrndrobwllllantysiliogogogoch
Privacy risks in data collection and storage
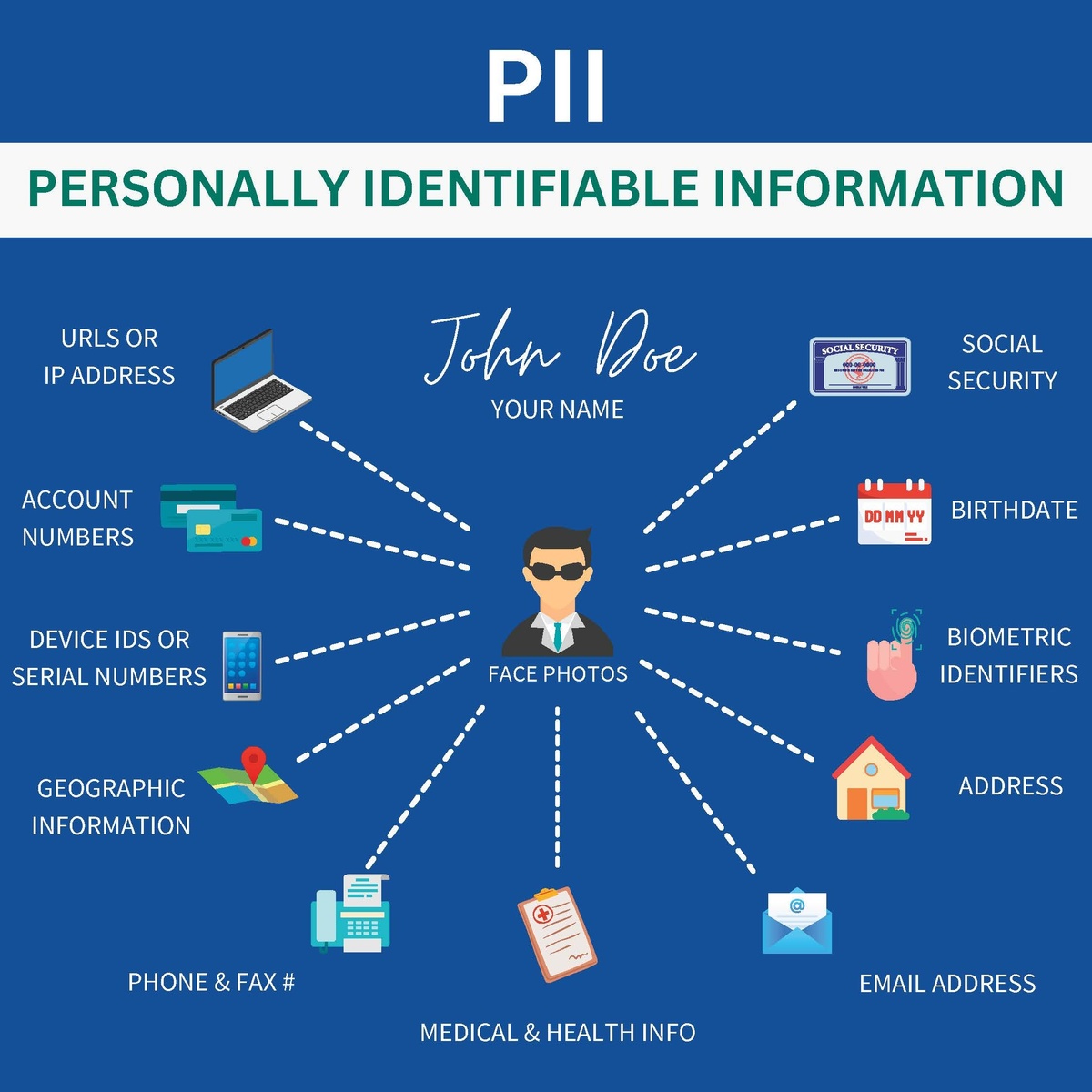
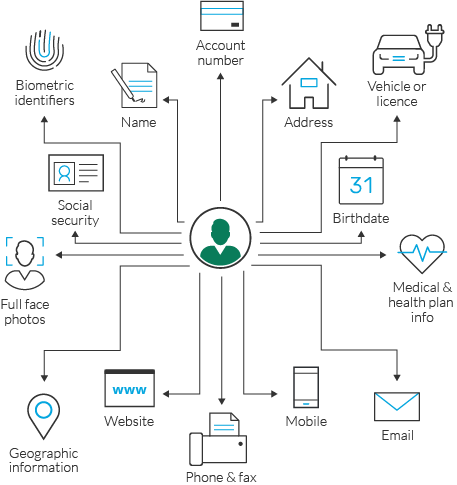
Companies collect data that can be used to identify their customers, called Personally identifiable information. This information often is necessary to fill orders, meet payroll, or perform other necessary business functions. PII is essential to identifying different users, both legally and illegally. The collection of PII gathered can often be a privacy threat. Organizations like companies, governments, and organizations utilize this data to analyze consumer behavior, political preferences, and personal interests.
Misuse and Protection of Computing Resource
Data privacy is the ensurement that data collected from individuals is collected legally, stored securely, and used for its intended purpose. This includes protecting personal information from unauthorized access, use, disclosure, modification, or destruction. Data privacy is essential to protect individuals from identity theft, financial fraud, and unauthorized surveillance, while enabling control over personal information. It ensures security, fosters trust between users and organizations, prevents malicious exploitation of data, and protects fundamental rights to privacy in a digital world.

Unauthorized Access to Information
Attackers launching cyberattacks often have goals in mind. An attacker uses human interaction to obtain or compromise information about an organization or its computer systems. They may impersonate someone who is trustworthy, even offering credentials to support that identity. By using these methods, attackers are able to piece together information that can be crucial to infiltrating an organization's network. These attackers aim to steal money, gain unauthorized account access, or install malware. Attackers use different methods in order to gain information. Phishing is a type of cyberattack where attackers impersonate trustworthy organizations to trick individuals into revealing sensitive information, such as passwords, credit card numbers, or login credentials.

Benefits and Risks of Computing Innovation
Advances in computing have made communication easy and convenient. Innovations such as email, video conferencing, instant messaging, and social media platforms allow people to share information regardless of geography. Platforms like Zoom or Microsoft Teams and social media networks enable people to share information instantly. These technologies have made efficient communication accessible to a wide range of people and have revolutionized how organizations and communities connect globally. Despite their benefits, these innovations present risks and challenges. Overuse of platforms may contribute to physical issues such as eyestrain, wrist pain, and sleep disruption. Social media allows anyone to post content, which can contribute to the spread of misinformation. Additionally, data shared on messaging apps or social networks can be accessed or misused by malicious actors, potentially leading to identity theft or financial fraud. Users must be mindful of how they use these technologies, balancing connectivity with healthy boundaries to protect both mental and physical well-being. Technology is not objectively good or bad. Its value depends on how you use it. It is important to use technology in moderation. While technology can improve efficiency and connect many people, excessive use can lead to many negative effects.
